
Nos mercados dos EUA e da Europa, o hardware RFID não é avaliado apenas pelo desempenho. Os compradores esperam rastreabilidade, proteção contra clonagem e conformidade com regulamentações de privacidade de dados, como o GDPR. Para varejistas, organizadores de eventos e gestores de ativos industriais, o verdadeiro limite de segurança não é a plataforma de software. Ele é definido pelo chip escolhido, pelo material utilizado e pela forma como o fornecedor fabrica e codifica os produtos.
A seguir, explicamos como as decisões tomadas em nível de hardware protegem diretamente seus ativos e seus dados.
O Silicon Shield: a segurança em nível de chip começa no UID.
A segurança RFID começa no nível do chip. Padrões como:
• ISO/IEC 14443 (cartões e pulseiras sem contato)
• ISO/IEC 18000-6C / EPC Gen2 (etiquetas RFID UHF)
Definir não apenas os protocolos de comunicação, mas também como os recursos de segurança são implementados no silício.
O que implementamos no nível do chip:
1) Identificador único (UID) bloqueado de fábrica
Cada chip contém um UID não regravável. Isso cria uma identidade baseada em hardware que não pode ser duplicada por meio de codificação padrão.
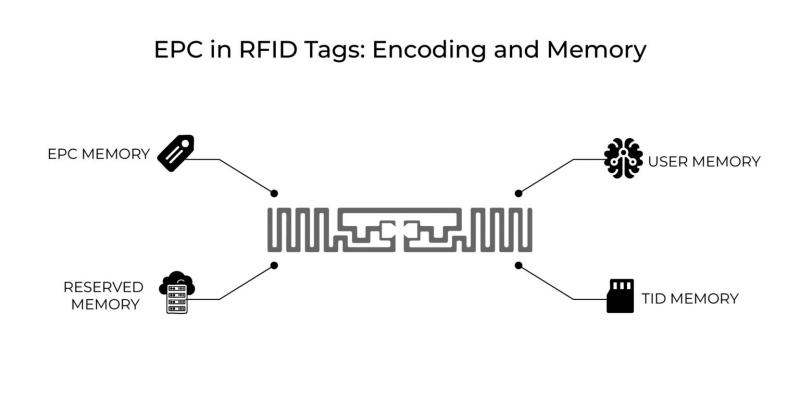
2) Segmentação de memória e proteção por senha
Configuramos os chips com:
• Senhas de acesso (controle de leitura/gravação)
• Eliminar senhas (desativação permanente)
• Bancos de memória bloqueados (EPC, TID, Memória do Usuário)
Isso garante que leitores não autorizados não possam sobrescrever ou extrair dados confidenciais.
3) Recursos anti-clonagem (dependentes do chip)
Suporte para circuitos integrados avançados (por exemplo, da NXP ou Impinj):
• Autenticação criptográfica
• Identificadores aleatórios (para casos de uso que exigem atenção à privacidade)
Suas etiquetas não apenas transmitem dados — elas controlam quem tem permissão para acessá-los.
Integridade física para proteção de ativos
A segurança não se limita ao chip. A estrutura física dos produtos RFID desempenha um papel direto na prevenção de adulteração e reutilização não autorizada.
Pulseiras RFID (Controle de Eventos e Acesso)
Projetamos pulseiras com mecanismos de travamento de uso único:
• Sistemas de fechamento unidirecional que não podem ser reabertos sem sofrer danos
• Estruturas quebráveis que indicam visivelmente adulteração
Uma vez aplicada, a credencial permanece vinculada a um único usuário. Isso impede o compartilhamento ou a revenda da credencial.
Cartões RFID (Varejo e Associação)
Para cartões em conformidade com a norma ISO/IEC 14443:
• Estruturas multicamadas de PVC/PET protegem a antena e o chip integrados.
• A laminação resiste às tentativas de delaminação utilizadas para acessar componentes internos.
• Camadas de proteção opcionais podem ser adicionadas para bloquear a leitura não autorizada.
Seus dados permanecem fisicamente protegidos, mesmo sob estresse ou uso indevido.
Etiquetas RFID invioláveis (Rastreamento de Ativos)
Para aplicações industriais e logísticas:
• Substratos frágeis interrompem a continuidade da antena quando removidos.
• Adesivos destrutivos impedem uma transferência limpa
• Padrões ou resíduos de tinta VAZIA fornecem evidências visíveis de adulteração.
Se alguém tentar remover a etiqueta, ela para de funcionar.

Serviços de fabricação e codificação seguras
A segurança do hardware fica comprometida no momento em que a codificação é feita de forma inadequada. É por isso que tratamos o processamento de dados durante a produção como um processo controlado.
Nosso fluxo de trabalho de codificação:
1) Transferência de dados criptografados
Os dados do cliente são transmitidos por canais seguros. Não aceitamos arquivos não criptografados para codificação.
2) Minimização e mascaramento de dados
Processamos apenas os campos obrigatórios. Os conjuntos de dados sensíveis são segmentados e mascarados sempre que possível.
3) Ambiente de codificação controlada
• Estações de codificação dedicadas (sem exposição à rede aberta)
• Operadores com acesso restrito
• Rastreabilidade em nível de lote para cada produto codificado
4) Verificação antes do envio
Verificamos o mapeamento de dados UID, o status de bloqueio e a precisão da codificação antes da entrega.
Codificamos os dados na fábrica para que seus produtos cheguem prontos para uso, sem expor seus dados a riscos de terceiros.
Navegando pelo RGPD com recursos de hardware
A conformidade com o RGPD é frequentemente discutida no nível do software, mas os recursos de hardware dão suporte direto às estratégias de conformidade.
Principais funções de privacidade com suporte de hardware:
1) Comando de desativação (etiquetas UHF)
Compatível com a norma ISO/IEC 18000-6C, permite a desativação permanente de uma etiqueta utilizando uma senha segura.
Caso de uso:
Desative as etiquetas de preço no ponto de venda para evitar o rastreamento após a compra.
2) Modos de privacidade/não rastreáveis (dependentes do chip)
Alguns chips suportam:
• Ocultar dados EPC
• Limitar as respostas a leitores autenticados
Isso reduz o risco de rastreamento não autorizado em ambientes públicos.
3) Materiais de blindagem
Oferecemos camadas opcionais de bloqueio de radiofrequência para cartas e capas:
• Impedir leituras acidentais quando não estiver em uso
• Adicione uma camada extra de privacidade controlada pelo usuário
4) Projeto de faixa de leitura controlada
Ajustando o tamanho e a sensibilidade da antena, podemos:
• Limitar a distância de leitura
• Reduzir varreduras de longo alcance não intencionais
O RGPD não se limita ao tratamento de dados — trata-se da prevenção da exposição de dados, começando pelo hardware.
Uma “Verificação de Especificações” Prática para Compradores
Ao analisar produtos RFID, a maioria das fichas técnicas são semelhantes. Concentre-se nos seguintes parâmetros relacionados à segurança:
Categoria | O que verificar | Por que isso importa |
Tipo de chip | NXP / Impinj / equivalente | Determina os recursos de segurança disponíveis. |
UID | Bloqueado de fábrica / não regravável | Impede a clonagem de identidade |
Bloqueio de memória | Suportado (EPC / Usuário / TID) | Protege os dados armazenados |
Senhas | Senhas de acesso e desativação disponíveis | Controles de leitura/gravação e desativação |
Projeto de adulteração | Frágil / destrutível / de uso único | Impede a reutilização física. |
Serviço de Codificação | Seguro, interno | Reduz o risco de vazamento de dados |
Conformidade | ISO/IEC 14443 ou 18000-6C | Garante a interoperabilidade e o alinhamento com os padrões. |
Recursos de privacidade | Eliminar / Irrastreável / Proteger | Suporta a conformidade com o RGPD (Regulamento Geral sobre a Proteção de Dados). |
Nota final
A segurança não é um recurso adicional. Ela está integrada ao hardware desde o início.
Fabricamos etiquetas, cartões e pulseiras RFID com proteção em nível de chip, estruturas resistentes a adulteração e processos de codificação controlados — para que sua implementação esteja segura antes mesmo de entrar em operação.
Se sua aplicação envolve dados de clientes, controle de acesso ou ativos de alto valor, a escolha do hardware não é apenas uma decisão de aquisição. É uma medida de controle de riscos.
Bate-papo agora
Digitalizar para Wechat :

Digitalizar para WhatsApp :
